Between National Cybersecurity Awareness Month and current events, you’re probably hearing a lot about people trying to cause trouble (or affect elections) using the internet lately. Companies and individuals face millions of cybersecurity threats every day, from corporate espionage to identity theft.
Colorado is home to a massive amount of cybersecurity companies who are diligently working to fight off these attackers and prevent them in the first place. We caught up with three of Colorado’s premier cybersecurity companies to learn more about the “bad guys” they’re fighting and how they’ve managed to pull it off.

Responses provided by ProtectWise’s threat team: James Condon, Director of Threat Research; Tom Hegel, Threat Researcher; and Michael Logoyda, Network Security Research Engineer.
Who are the "bad guys" ProtectWise fights against?
Malicious actors on the internet. Specifically, individuals and organizations looking to steal intellectual property, steal banking information, profit from others’ resources or work or embarrass and slander organizations for political objectives.
What does ProtectWise do to fight them?
We work to expose their activities by detecting their actions on customer networks. Exposing their tactics and monitoring their infrastructure gives potential victims the tools they need to respond to these attacks.
Has that always been the company's mission, or was it developed somewhere along the way?
Always been part of the company mission.
What are some of your big successes, qualitatively?
We've helped customers establish timelines for attacker activities spawning several months, enabling them to avoid costly, outsourced incident response scenarios. We've helped a customer thwart the compromise of a company bank account before damage was done. We've helped victims of ransomware identify the source of the infection and given guidance on how to prevent it in the future. We've helped customers respond to higher authorities auditing them for evidence of certain campaigns affecting their industry. We've identified customers’ web servers being used for command and control for larger malware campaigns. And we've identified several victims who had their personal and corporate credentials stolen.
Responses provided by Tyler Moffitt, Senior Threat Research Analyst
Who are the "bad guys" Webroot fights against?
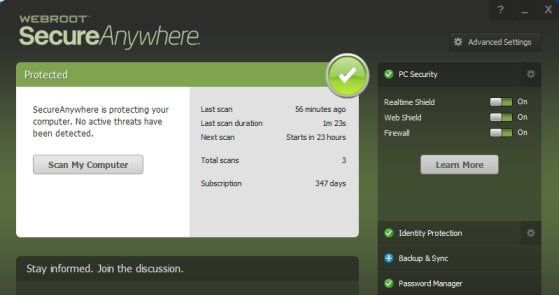
From phishing scams and identity thieves targeting your banking, shopping and social media information to highly organized cybercriminals trying to steal classified corporate data, Webroot defends against cyberattacks of all types on Windows, Android and Mac devices.
What does Webroot do to fight them?
Webroot delivers next-generation security and threat intelligence services in a layered approach to protect businesses and individuals in a connected world. All Webroot solutions are powered by the self-learning Webroot® Threat Intelligence Platform, which can identify never-before-seen threats by examining how they act, where they come from, where they’ve been and which other internet items they’re associated with to provide predictive cloud-based protection.
Has that always been the company's mission, or was it developed somewhere along the way?
Webroot’s mission has developed over time. As more and more devices begin to connect to the internet, protecting them is more crucial than ever. Next-gen malware is here and Webroot strives to be the leader in next-generation security and threat intelligence services to protect all users everywhere in the world.
What are some of your big successes, numbers-wise?
On an average day, Webroot finds over 6,000+ new phishing sites, more than 25,000 new malicious URLs, 100,000+ new malware and potentially unwanted apps (PUAs) and 1,000,000+ new file encounters.
What are some of your big successes, qualitatively?
Our machine learning and collective threat intelligence. Because every Webroot-protected device around the globe is connected to the Webroot® Threat Intelligence Platform, any time a new threat is encountered by one Webroot customer, every other customer is protected in real time. Whenever a Webroot security solution is deployed on a new device, our threat intelligence gets smarter. Tens-of-millions of sensors worldwide continually identify new malware and learn new tactics that hackers use to steal data.

Responses provided by Greg Foss, Security Operations Manager
Who are the "bad guys" LogRhythm fights against?
LogRhythm fights against adversaries of all shapes and sizes, including ransomware infections, fraud, insider threats, data exfiltration, and the internet’s most advanced attackers. The bad guys are constantly improving upon their techniques and developing new ways to evade an organization’s detection capabilities. As such, LogRhythm is constantly improving upon the methods we use to detect such attacks.
What does LogRhythm do to fight them?
LogRhythm uses artificial intelligence and machine learning-based techniques to give organizations enhanced visibility into their data. By utilizing indicators associated with the adversaries’ Tactics, Techniques and Procedures (TTP) to trigger alerts on anomalous activity, LogRhythm can actively defend the network and dynamically respond to threats. Simultaneously, we gather forensic information from all of the various devices on the network so we’re constantly improving our services and staying ahead of the “bad guy.”
Has that always been the company's mission, or was it developed somewhere along the way?
LogRhythm was founded on the idea of protecting organizations by way of fully realizing the potential of log and network forensic data correlation across the enterprise. It’s a complex mission, and — as technology evolves to deliver more efficiency — it continues to hold true.
What are some of your big successes, numbers-wise?
LogRhythm has more than 2,800 customers in the financial services, retail and hospitality, energy/utilities, higher education, healthcare and government industries worldwide. Strong demand for its Security Intelligence and Analytics Platform has propelled the company to record customer growth.
What are some of your big successes, qualitatively?
We have seen a number of organizations use forensic data from LogRhythm’s Security Information and Event Management (SIEM) platform to discover other threats that would have previously gone unnoticed. On top of the many unique attacks detected and stopped by LogRhythm, customers have been able to passively detect malware as it traverses their network; this provides an additional layer of protection for those hosts that either don't have antivirus installed or for when a detection is missed for whatever reason. In addition to security issues, operational issues and vulnerabilities can be passively detected as well — often exposing a misconfiguration or authentication failures that are causing accounts to lock out.
Photos via featured companies. Responses have been edited for length and clarity.
Have a tip or know of a company that deserves coverage? Email us.



